OAuth
Authorization protocol that lets apps access user data without sharing passwords.
Authorization protocol that lets apps access user data without sharing passwords.
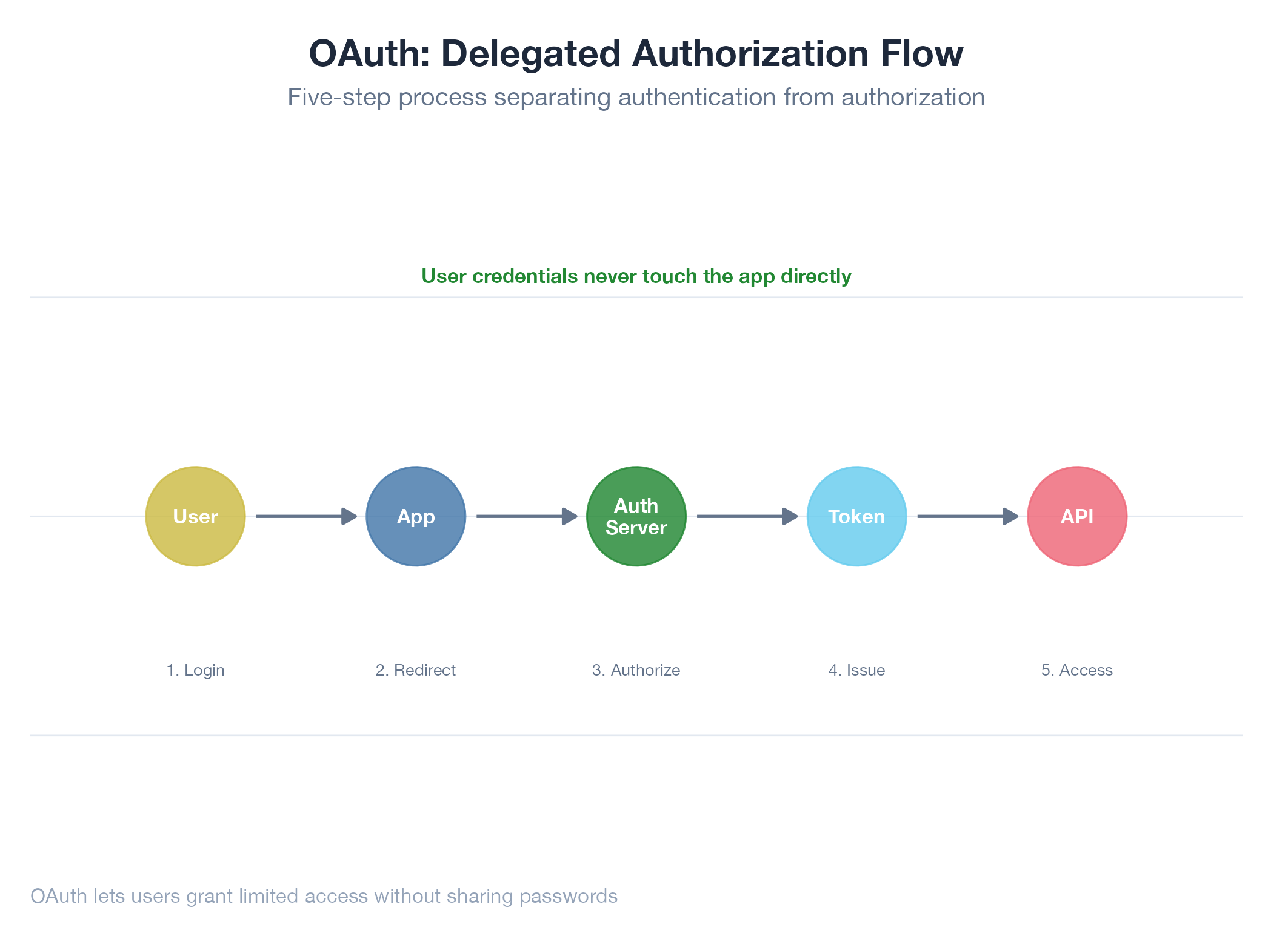
OAuth is a delegation protocol: instead of giving an app your password, you tell the service “yes, this app can read my email” and the service hands the app a time-limited token: a hotel key card that opens your room but not the staff office. The app never sees your credentials. OAuth 2.0 defines several flows; the most common is authorization code + PKCE: redirect to the service’s login page → consent → get a short-lived code → exchange it for access and refresh tokens. Access tokens expire (typically 1 hour); refresh tokens let the app renew them silently.
How It Works
Four steps: Redirect (app → service login with scopes) → Consent (user approves) → Code (service redirects back with a one-time code) → Token (app exchanges code + own credentials for tokens). PKCE prevents interception of the authorization code.
Example
The jobs-apply Gmail OAuth pipeline grants read access to classify inbox emails, match them to applications, and update the state machine. Google Cloud credentials (client_id and secret in config/default.yaml) with specific scopes. First crawl: 46 updates, 5 interviews, 41 rejections. Detailed at Jobs Apply Gmail Pipeline.