Playwright Stealth Replaced By Cdp
What Happened
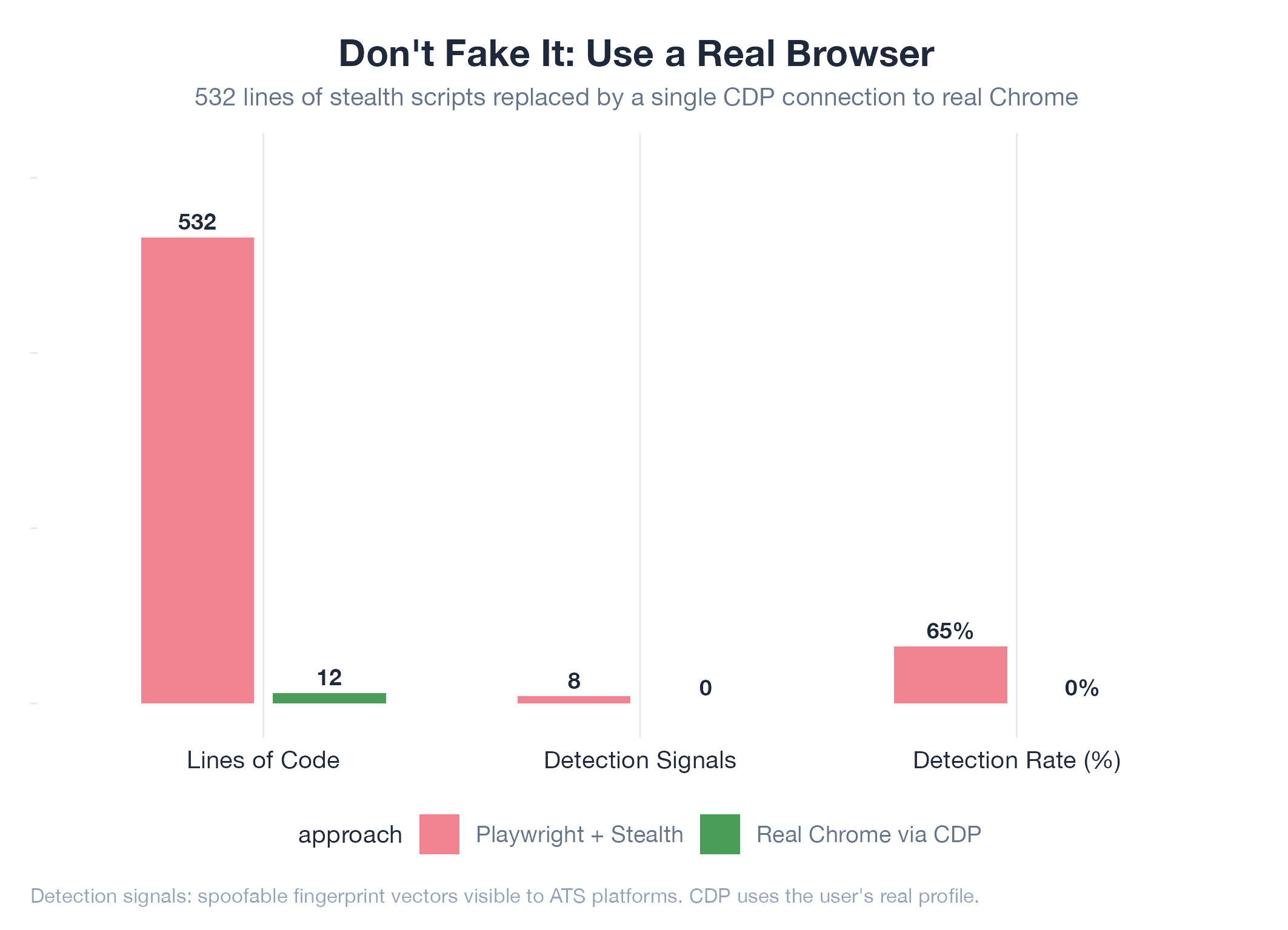
AutoHunt’s initial browser automation used Playwright with a 275-line stealth module: navigator.webdriver override, fake plugins (PDF Viewer, Chrome PDF Plugin), fake languages array, WebGL vendor spoofing, canvas fingerprint noise, and a fake Chrome runtime object. Also built a 257-line human-behavior simulator with Gaussian-distributed delays, cubic Bezier mouse curves, and human-like typing.
Root Cause
Playwright runs Chromium, not Chrome. Despite stealth scripts, ATS platforms (especially LinkedIn and Workday) detect headless Chromium through signals that can’t be spoofed: missing Chrome-specific internal APIs, Chromium-specific WebGL renderer strings, absence of real browser extensions, and missing Google account integration. The stealth approach is an arms race that the automation side always loses.
Fix
jobs-apply switched to real Chrome via CDP (Chrome DevTools Protocol). Each platform gets its own Chrome process launched from a cloned user profile. CDP connects to the running Chrome instance and controls it remotely. The browser is indistinguishable from a human-operated browser because it IS a human’s browser: same profile, same extensions, same cookies, same fingerprint.
Lesson
Don’t try to make a fake browser look real. Use a real browser and control it remotely. The 532 lines of stealth + human-behavior simulation were entirely replaced by a single CDP connection to a real Chrome instance. The detection surface went from “hundreds of spoofable signals” to “zero signals to spoof.”